Cybersecurity for Law Firms
 Cybersecurity for Law Firms is critical for law firms’ protection of sensitive client data against sophisticated cyber threats.
Cybersecurity for Law Firms is critical for law firms’ protection of sensitive client data against sophisticated cyber threats.
This article simplifies the complex cybersecurity landscape, highlighting the vulnerabilities, legal responsibilities, and effective strategies necessary for law firms to safeguard their information.
Along with these strategies, we’ll discuss how IT support, especially Practice Next, can be surprisingly effective for handing off some of these responsibilities to providers who have invested heavily in secure data management.
Keep reading to discover how your law firm can navigate and overcome these cyber challenges, ensuring robust protection for your clients and your practice in the digital landscape.
Introduction to Cybersecurity for Law Firms
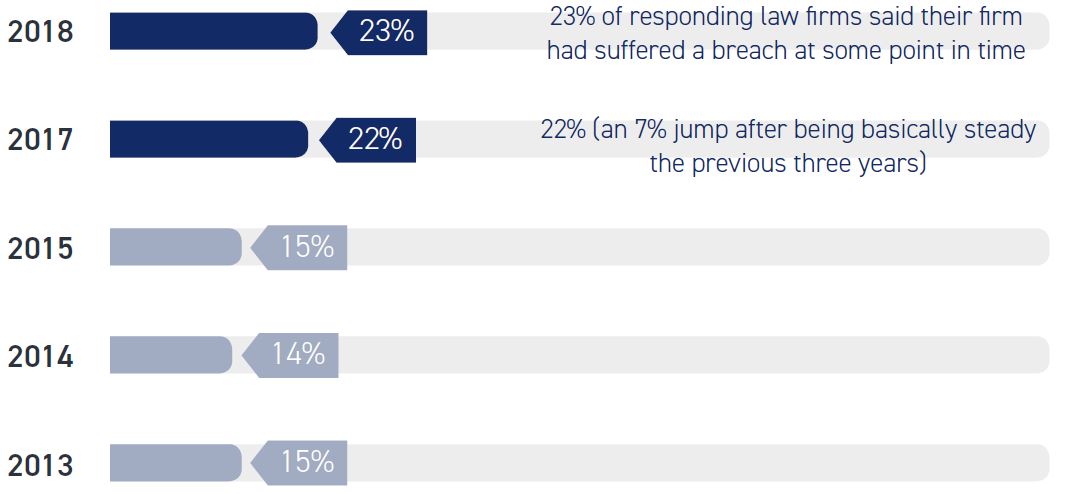
In response to the American Bar Association’s (ABA) survey, 29% of law firms responded saying they experienced a security breach.
Cybersecurity has become a cornerstone concern for every industry but is particularly important for law firms. Since you are entrusted with safeguarding highly sensitive client information, you’re now a target for cybercriminals and must take proactive measures.
Embracing robust cybersecurity strategies is now a fundamental aspect of legal practice, integral to maintaining client trust and upholding professional standards. I understand that this sounds like a lot of responsibility and intricacy for a law firm that would rather serve clients than manage their cybersecurity.
However, by choosing optimal practices and a trusted IT partner, your data can be exponentially more secure than in-house storage.
Keep in mind that cybersecurity is a vital aspect to keeping the lights on and your clients protected, so let’s set up a plan for your law firm.
Related – IT Support for Law Firms: Having readily-available support relieves the burden and stress of law firms’ technology stack. Learn more.
Security & Compliance are Non-Negotiable for Law Firms
With Uptime Practice Next, get:
- Multi-Factor Authentication
- Email Encryption
- Compliant Backups
- Desktop Protection
- Ransomware Protection
- and More!
Cybersecurity Risks for Law Firms
Since digital information is now as valuable as physical assets (if not more so), law firms face a myriad of cybersecurity threats. Cybercriminals often target law firms due to the wealth of sensitive client information they hold, ranging from personal data to confidential business matters.
These threats are not just technologically advanced but are also becoming more sophisticated in their approach.
With this in mind, let’s cover some of the risks that you need to be aware of, so you’ll be prepared to defend your firm.
Phishing Attacks
According to the 2025 Verizon Report, phishing and other human-related incidents are responsible for 60% of breaches.
These attacks often come in the form of deceptive emails, purporting to be from legitimate sources and find most success with untrained employees.
They aim to extract sensitive information such as login credentials or personal client details. Law firms, with their wealth of confidential data, are particularly attractive for phishers.
A managed IT provider can help train your employees to avoid these slipups, and if they happen anyway, they can help you recover your data and build the firewall back up.
The impact of such attacks can range from financial loss to severe damage to the firm’s reputation.
Insider Threats
These can occur when employees or contractors misuse their access to firm resources. This might be due to malicious intent, such as stealing client information, or simple carelessness, like falling for phishing scams.
Data Breaches
These breaches can occur due to external hacking attempts or internal security lapses.
The consequences include legal liabilities, financial penalties, and loss of client trust. Breaches can result from weak security protocols, unpatched software vulnerabilities, or inadequate network security.
Managed cloud services can help keep these from happening by hosting your software on servers that are more secure than what you could have in office.
Advanced Persistent Threats (APTs)
These are prolonged and targeted cyberattacks in which an intruder gains access to a network and remains undetected for an extended period.
APTs can be particularly damaging as they allow continuous access to sensitive information.
Ransomware
This type of malware encrypts a victim's data, holding it hostage until a ransom is paid.
For law firms, the implications are dire: lost access to critical files can halt legal proceedings and compromise sensitive cases.
Even if the ransom is paid, there’s no guarantee that the data will be fully recovered.
Having knowledgeable IT support can come in handy if you ever find yourself in this situation, as well as work to keep it from happening in the first place.
This list is not meant to make you fearful. In fact, I’m hoping you’ll respond with justified vigilance rather than fear.
I know it may sound like you’re fighting a battle at a disadvantage, but you’re really capable of keeping your law firm safe with proper measures.
With that being said, don’t be like the 47% of law firms that don’t have specific policies tied to disaster recovery and business continuity (Source: ABA). Be the 53% who does! You won’t regret it.
Related – Law Firm Disaster Recovery: Law firms must be proactive in their approach to law firm disaster recovery & business continuity planning. Read this article to learn more.
Legal and Ethical Duties as a Law Firm
I don’t have to tell you, someone from a law firm, how important the legal and ethical responsibilities surrounding cybersecurity are. Failing to take proper measures could lead to lawsuits and distrust in the communities you serve.
Law firms are inherently bound by a duty of confidentiality and a responsibility to protect client information, a mandate that extends to digital data.
Let’s cover what that entails.
Confidentiality Obligations
The American Bar Association (ABA) and other legal bodies worldwide underscore the need for attorneys to safeguard client information.
This includes ensuring that electronic communications and stored data are secure from unauthorized access.
Supervision and Training
Law firms must ensure that their staff, including both lawyers and support personnel, comply with appropriate cybersecurity practices.
This includes training employees to recognize and adequately handle cyber threats like phishing scams.
Data Protection Laws
Various jurisdictions have stringent data protection laws, such as GDPR in Europe and state-specific laws in the U.S. like California’s CCPA.
These regulations impose obligations on law firms to protect personal information and report any data breaches in a timely manner.
Ethical Considerations
Beyond legal requirements, there are ethical considerations.
Law firms must adopt a culture of cybersecurity awareness and practice due diligence in protecting client data. This is essential not only for compliance but also for maintaining client trust and the firm's reputation.
Consequences of Non-Compliance
Failure to comply with these legal and ethical standards can lead to severe consequences, including legal action, fines, and damage to the firm's reputation.
Understanding these principles is not just a matter of legal compliance but also a cornerstone of ethical practice and client trust.
As the digital landscape evolves, so too must the approaches law firms take to protect sensitive information. This commitment to cybersecurity is a reflection of a firm’s dedication to its clients and the integrity of the legal profession itself.
Don’t forget — as technology advances, so do cyber-attacks. Take a look at these statistics from the ABA Legal Technology Survey Report.
Cybersecurity Tips for Law Firms
Adopting best practices in cybersecurity is not merely a reactive measure; it’s a proactive strategy essential for the modern law firm.
This section provides helpful tips that law firms should implement to strengthen their defense against digital threats, ensuring the security of their data and the trust of their clients.
Let’s explore these practices, which range from risk assessments to incident response planning, each a critical piece in the cybersecurity puzzle.
Conduct Regular Cybersecurity Risk Assessments
Regular assessments help identify vulnerabilities in the firm’s IT infrastructure.
These assessments should include checking for potential threats, evaluating the effectiveness of current security measures, and identifying areas for improvement.
Develop a Comprehensive Cybersecurity Policy
A robust policy sets the standard for data handling and security within the firm.
It should cover aspects like data encryption, secure file sharing, and incident reporting protocols.
According to the ABA, only 42% of respondents have an incident response plan, and the smaller the firm, the less likely they are to have an incident response plan.
Implement Strong Password Policies and Multi-Factor Authentication (MFA)
Strong, unique passwords and the use of MFA add layers of security.
MFA requires users to provide two or more verification factors to gain access to resources, reducing the likelihood of unauthorized access.
Employee Training and Awareness Programs
Human error remains one of the biggest cybersecurity risks.
Regular training sessions can educate employees about the latest cyber threats, phishing scams, and safe internet practices. Emphasizing the importance of strong passwords and the dangers of using unsecured networks is critical.
According to the ABA, training is significantly less available at smaller law firms than larger law firms.
Regularly Update and Patch Systems
Keeping all software and systems up to date with the latest security patches is vital.
Outdated software can have vulnerabilities that are easily exploited by cybercriminals.
If you decide to outsource your IT or software hosting, your provider may offer these updates as part of their services.
Secure Wi-Fi Networks
Ensure that the firm’s Wi-Fi network is secure, encrypted, and hidden. Educate employees on the risks of using public Wi-Fi for work-related tasks.
Data Encryption
Encrypt sensitive data both in transit and at rest. This ensures that even if data is intercepted or accessed by unauthorized persons, it remains unreadable.
The ABA Survey reported that 49% of respondents utilize file encryption. This number is way too low for such an important method of cybersecurity.
Vendor Management
Assess the cybersecurity measures of third-party vendors.
Ensure they comply with the firm's cybersecurity standards, especially those who handle sensitive information.
Opt for No In-House Servers
Maintaining your own servers in-house increases your risk of a data breach since you're responsible for properly maintaining and protecting servers.
Oftentimes, we find that law firms keep their servers unprotected in some closet or copy room. What could go wrong?
Beyond data insecurity, you could also face server failure.
Server failures not only disrupt daily operations but can lead to the loss of crucial legal documents and client information.
For example, take a look at the chart below to understand what server ownership means for your firm over the course of the next 7 years.
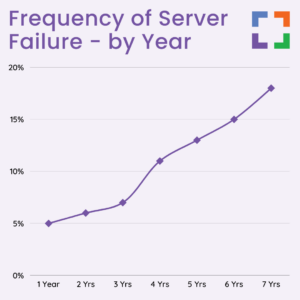
As you can see, not only do servers require a substantial upfront investment, but the frequency of server failure starts at 5% and increases with each year. At the 4-year mark, the chance of failure more than doubles and nears 20% by the 7th year.
For becoming serverless, we recommend either opting for cloud-based software or finding a cloud-host, such as Uptime Practice, to store and manage your server-based software on your behalf.
Backup and Disaster Recovery Plans
Regular backups and a solid disaster recovery plan ensure that in the event of a data breach or loss, the firm can quickly restore lost data and maintain business continuity.
This is a specialty of managed service providers, like those who provide service through Uptime Practice Next.
Find Prompt, Reliable IT Support
Efficient and timely IT support is crucial for addressing and mitigating cybersecurity threats.
The absence of reliable IT support can leave a law firm vulnerable to ongoing attacks and unable to quickly respond to and recover from incidents. This delay can exacerbate the impact of cyber threats, leading to greater data loss and reputational damage.
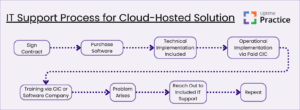
Take a look at the flow chart below to understand the process you would have to go through each time you need new software, new servers, updates, or general support.
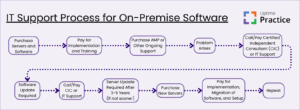
However, if you decide to pursue a cloud-hosted solution, your setup process is simpler and your IT support is both easily and readily available.
By integrating these cybersecurity best practices, law firms can significantly elevate their defense mechanisms against the ever-changing cyber threats.
These measures go beyond mere compliance; they embed a culture of security within the firm.
With the right approach to cybersecurity, law firms not only protect their sensitive data but also fortify their reputation and trust in the community.

Uptime Practice was a true miracle when the pandemic struck. We moved to Uptime Practice and were working immediately.
Todd Tracy – The Tracy Law Group, PLLC
Next Steps for Your Law Firm's Cybersecurity
As law firms navigate the complexities of cybersecurity in the digital era, taking proactive steps is essential.
The journey towards enhanced cybersecurity involves several key actions:
1
Evaluate Current Cybersecurity Posture
Begin by conducting a thorough assessment of your firm’s existing cybersecurity measures.
This includes reviewing current security protocols, software, hardware, and employee cybersecurity awareness. Identifying vulnerabilities and areas for improvement is critical in shaping an effective cybersecurity strategy.
2
Develop a Comprehensive Cybersecurity Plan
Integrate the insights and best practices discussed into a detailed cybersecurity plan.
This should encompass policies on data protection, incident response, risk management, and compliance with legal standards.
3
Implement Cloud-Based Solutions
Transition to private cloud services for better security and operational efficiency.
Cloud solutions offer advanced security features, data encryption, and remote access, making them ideal for modern law firms seeking to enhance their cybersecurity infrastructure.
4
Partner with Specialized IT Support
Engage IT support providers who specialize in legal technology and cybersecurity.
These experts can offer tailored solutions, ongoing support, and proactive monitoring to address the unique cybersecurity needs of your law firm.
5
Regular Training and Awareness
Develop ongoing training programs to educate your staff about cybersecurity.
Regular updates on new threats, best practices for data handling, and training on identifying phishing attempts are crucial in building a security-conscious culture within your firm.
6
Stay Informed and Agile
Keep up to date with the latest cybersecurity trends, threats, and technological advancements.
Being agile allows your firm to adapt quickly to new threats and implement the latest cybersecurity measures to protect client data effectively.
By following these steps, law firms can ensure a successful migration to managed cloud services, positioning themselves for enhanced efficiency and growth.
Frequently Asked Questions
Law firms commonly face threats like phishing attacks, ransomware, data breaches, insider threats, and attacks exploiting IoT vulnerabilities.
Cloud-based solutions offer enhanced security features such as advanced encryption, secure data storage, regular updates, and comprehensive IT management, reducing the risk of cyberattacks.
Regular training helps employees recognize potential cybersecurity threats like phishing and adopt safe practices, reducing the risk of breaches due to human error.
Dedicated IT support provides specialized knowledge in legal software, continuous monitoring, timely technical assistance, and proactive management of cybersecurity threats.
Yes, private clouds provide secure, managed environments with robust cybersecurity measures, making them less vulnerable to attacks compared to traditional server setups.
After a breach, a law firm should activate its incident response plan, contain the breach, assess the damage, notify affected parties, and work on recovery and prevention of future incidents.
Law firms should regularly review and update their cybersecurity strategies to adapt to evolving threats and emerging technologies.
Yes, compliance with data protection laws like GDPR is crucial for law firms, especially those handling personal data of clients from regions where such regulations apply.
Uptime Practice:
The IT & Cloud Platform for Law Firms.
Uptime Practice is a suite of Managed IT and cloud services, made exclusively for law firms.
Practice Next
Technology + Legal Software Support for Modern Law Firms
Practice Next is a suite of Managed IT, Legal Software Support, and Cloud Essentials, made just for law firms.
-
Practice Next is a suite managed IT, technology essentials and legal software support.
-
Practice Next includes unlimited IT and legal software support, Microsoft 365, legal-centric cloud storage and more.
-
Practice Next pairs great with cloud-based legal software such as Clio Manage, CosmoLex, MyCase and more.
Practice Go
Cloudify Your Legal App
Does your law firm already have a cloud strategy, but have one premise-based application still running on onsite servers? Practice Go is for you.
- With Practice Go, we effectively turn your desktop/server- based legal software into a cloud application (a Published App), freeing your firm from the limitations of traditional software.
- Practice Go can cloudify your PCLaw, Time Matters, Tabs3, ProLaw, Juris, QuickBooks and more.
Practice Foundation
Complete Private Cloud for Law Firms
If your law firm needs a central, secure cloud platform for all of your legal software, documents and data, Practice Foundation is for you.
-
Practice Foundation is an end-to-end cloud platform that will host all of your firm's applications and documents, and will optionally include Office 365 + unlimited IT support. Everyone in your firm logs into a Virtual Desktop where they'll find all of their apps and docs.
-
Practice Foundation works with PCLaw, Time Matters, Tabs3, ProLaw, Juris, QuickBooks, Timeslips, TrialWorks, Adobe Acrobat and more.
Not Sure Which Edition You Need?
No problem. Check out our quick Comparison Chart for Uptime Practice, or Get in Touch to talk with our sales team.

Dennis Dimka
As the founder and CEO of Uptime Legal Systems, I've had the privilege of guiding our company to become a leading provider of technology services for law firms.
Our growth, both organic and through strategic acquisitions, has enabled us to offer a diverse range of services, tailored to the evolving needs of the legal industry.
Being recognized as an Ernst & Young Entrepreneur of the Year Finalist and seeing Uptime Legal ranked among the Inc. 5000 list of fastest-growing private companies in America for eight consecutive years are testaments to our team's dedication.
At Uptime Legal, we strive to continuously innovate and adapt in the rapidly evolving legal tech landscape, ensuring that law firms have access to the most advanced and reliable technology solutions.
Related Posts
January 20, 2025
5 IT Mistakes that Expose Law Firms to Cyber Threats
September 26, 2024
Outsourced but Onshore: Navigating Law Firm IT Regulations
June 27, 2024
The Impact of Remote Work on Law Firm IT
May 29, 2024
The Real Value of Legal Specialty in IT Services
April 24, 2024
Comparing Types of IT Providers for Law Firms
April 1, 2024
The Financial Case for Cloud for Law Firms
March 8, 2024
25 Things To Ask Your Legal Private Cloud Provider
March 5, 2024
How to Use ProLaw in the Cloud in 2025
February 28, 2024
Law Firm Disaster Recovery and Business Continuity Planning
February 22, 2024
Types of IT Services for Law Firms
February 8, 2024
Legal Data Management & Storage Solutions for Law Firms
February 1, 2024
How to Choose the Right IT Provider – A Guide for Law Firms
January 9, 2024
VoIP for Law Firms
January 8, 2024
How to Use Orion Legal Software in the Cloud in 2025
January 8, 2024
How to Use Time Matters in the Cloud in 2025
January 8, 2024
How to Use Juris in the Cloud in 2025
January 8, 2024
How to Use Tabs3 in the Cloud in 2025
January 8, 2024
How to Use TrialWorks in the Cloud
January 8, 2024
How to Use PCLaw in the Cloud in 2025
January 8, 2024
How to Use Timeslips & QuickBooks in the Cloud in 2025
December 15, 2023
How to Use Worldox in the Cloud in 2023
December 15, 2023
7 Reasons Your Law Firm Should Consider Tabs3
December 15, 2023
ProLaw Workspace – Review & Guide for Law Firms
December 15, 2023
TrialWorks – An Uptime Legal Review
December 8, 2023
Managed Cloud Services for Law firms
November 15, 2023
Outsourced IT for Law Firms
November 9, 2023
Managed IT Services for Law Firms
October 24, 2023
AWS for Law Firms: A Complete 101
October 11, 2023
IT Support for Law Firms
October 4, 2023
Azure for Law Firms: A Complete 101
September 28, 2023
Best Law Practice Management Software (2025)
September 5, 2023
Juris Support – How to Get Help for Juris
August 30, 2023
Tabs3 Support – How to Get Help for Tabs3
August 23, 2023
ProLaw Support – How to Get Help for ProLaw
July 24, 2023
PCLaw Support – How to Get Help for PCLaw
July 20, 2023
Private Cloud 101 for Law Firms
February 24, 2021
Uptime Legal Joins the Thomson Reuters Marketplace
November 18, 2019
Best Legal Practice Management Software for 2021
September 16, 2019
The Financial Case for Cloud for Law Firms
June 17, 2019
Law Firm IT – What Are Your Options?
June 10, 2019
5 Things to Require of Your Law Firm IT Provider
January 28, 2019
PCLaw® Go – An Uptime Legal Review
January 7, 2019
Time Matters® Go – An Uptime Legal Review
October 24, 2017